Announcing CMMC 2.0: An Overview of Changes
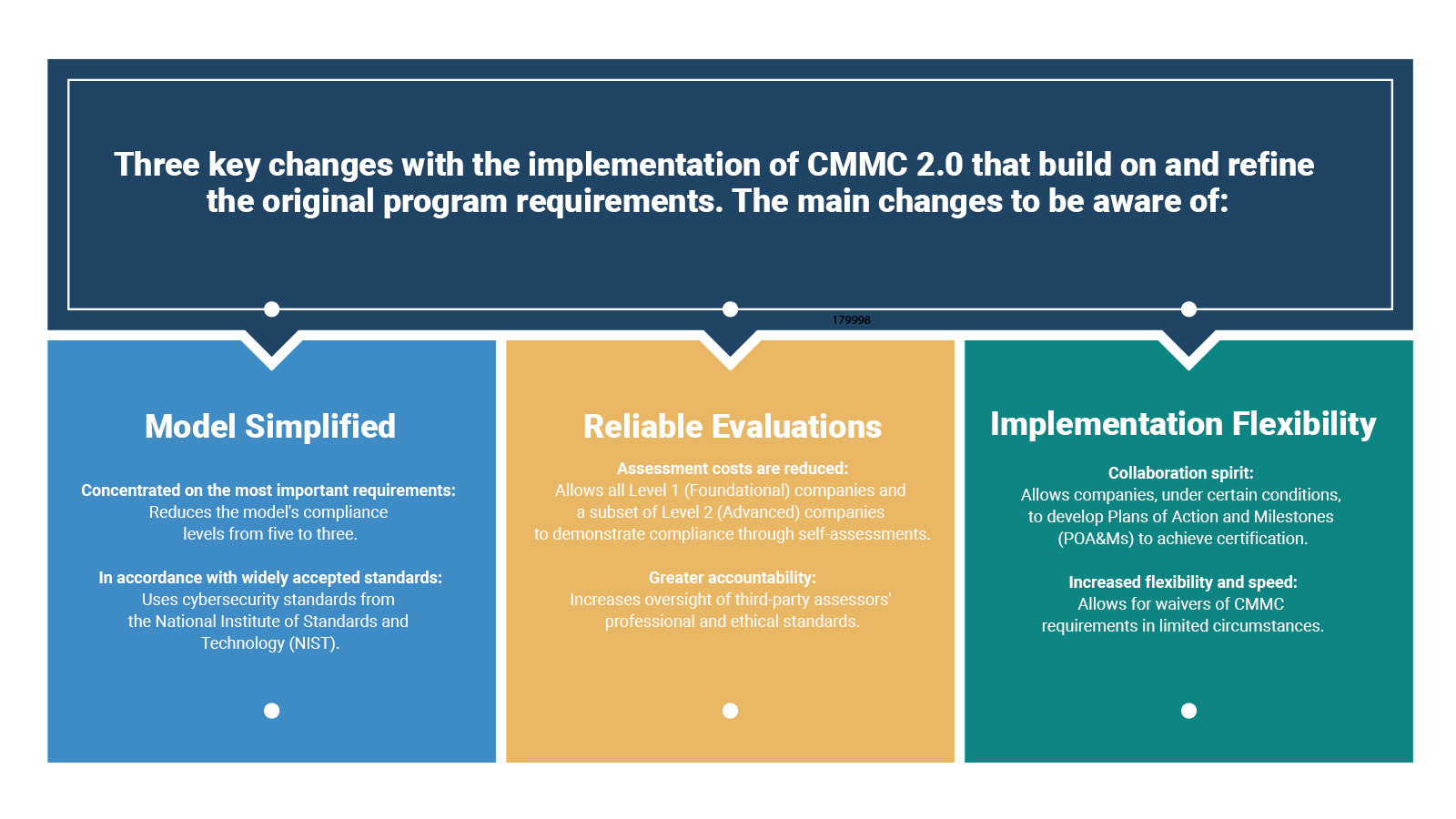
With the implementation of CMMC 2.0 announced November 4, 2021, the Department of Defense is introducing several key changes that build on and refine the original CMMC program requirements. While significant changes have been made, we are still awaiting the approval of several requirements in the program. The graphic below illustrates an overview of fundamental structure changes you can expect to see with version 2.0.
CMMC 2.0: Tiered Level Structural Changes
One of the most significant changes you’ll notice is the tiered level structure of CMMC 2.0. It is consolidated into just three levels: Foundational, Advanced and Expert.
Specifics to Note
- Levels 2 and 4 have been removed from the tiered structure
- CMMC unique practices and maturity processes have also been removed from the CMMC 2.0 model
- DoD has designated Level 3 as an expert level, allowing DIB contractors and subcontractors to conduct annual self-assessments that include an annual confirmation by DIB business leadership as part of Level 1.
- Expert Level 3 represents CMMC 1.0 Level 5 and is intended for DIB contractors & subcontractors that handle Controlled Unclassified Information (CUI.)
- Expert Level 3 will now include NIST 800-171 controls.
- A time-bound, selective waiver process for the entire CMMC requirement, not individual controls. These waivers will be granted by DoD leadership on a case-by-case basis to expedite time-critical acquisitions when CMMC regulations may jeopardize mission-critical capabilities.
Plan of Actions and Milestones (POAMS)
The Department of Defense expects to allow contracts to be granted with a Plan of Actions and Milestones (POAM) in place to meet CMMC standards with CMMC 2.0. Several controls will be required for award, with additional controls to be addressed according to a clearly defined timeframe.
CMMC 2.0 Level 1: What It Means
The 17 controls of CMMC 1.0 Level 1, a limited subset of NIST 800-171 aimed for basic cyber hygiene, will be included in CMMC 2.0 Level 1. This only applies to organizations that deal with federal contracting information (FCI.) This basic level is seen by the government as an opportunity to involve contractors in creating and upgrading their cybersecurity posture. With a self-assessment, CMMC 2.0 Level 1 will be achieved.
CMMC 2.0 Level 2: What It Means
The 110 controls of NIST 800-171 are included in CMMC 2.0 Level 2. The criticality of the information possessed by the organization will determine how Level 2 is divided. A third-party evaluation will be required every three years for businesses that are found to have CUI classified as Critical National Security Information. A self-evaluation against these controls once a year will suffice for some firms.
What CMMC Level will my company require now?
For FCI handling organizations, this is greatly simplified as Level 1, removing the old transitional level that might be required for FCI.
For organizations handling CUI, the required CMMC level for contractors and subcontractors will be specified in Requests for Information and Solicitations. No CMMC requirements will be added to contracts until the formal rule-making process is complete.
Rulemaking Process and Approvals
The CMMC 2.0 changes will be implemented through the rulemaking process. Companies will be required to comply once the new rules take effect. The Department intends to pursue rulemaking in both Part 32 of the Code of Federal Regulations (C.F.R.) and Part 48 of the C.F.R. in the Defense Federal Acquisition Regulation Supplement (DFARS). Both rules will be subject to public comment. Stakeholder input is critical to meeting the CMMC program’s objectives, and the Department will actively seek opportunities to engage stakeholders as it moves toward full implementation.
While these rulemaking efforts are underway, the Department intends to halt current CMMC Piloting efforts and will not approve the inclusion of a CMMC requirement in any DoD solicitation.
The Department encourages contractors to continue to improve their cybersecurity posture. In the meantime, the DoD is looking into ways to provide incentives to contractors who voluntarily obtain CMMC certification. More to come in this area.
Projected Timeline
The DoD has specified that while the publication of CMMC 2.0 materials can be understood to reflect strategic intent, there will be no contractual requirements for CMMC 2.0 until formal rulemaking is complete. This process can take 9-24 months. (The time from the first published draft of CMMC to DFARS 7021 was approximately 22 months, as a benchmark.)
Your Next Steps
Continue strengthening your cybersecurity hygiene and best practices. CMMC is here to stay as a formidable requirement to simplify compliance and accelerate it. Consider these next steps to drive continued development of your security programs so that you’re ready when final rules are approved.
- The entire DIB is still subject to DFARS compliance, and you already have contractual requirements to meet NIST 800-171 and DFARS 7012, without the CMMC 2.0 changes.
- Solidifying the staying power of CMMC, the recent DOJ Cyber-Fraud initiative gives the DOJ the teeth and motivation to pursue false claims act charges against federal contractors who have not met their contractual cybersecurity requirements.
- Take a deep breath and keep working to effectively prepare for your CMMC certification. There is still time to plan and prepare with the new 2.0 timeline. The DFARS 7021 requirement to submit and maintain a NIST 800-171 self-assessment in the DoD’s Supplier Performance Risk System (SPRS) still stands, and your organization will still be responsible for this.
Get started on your self-assessment and continue with your CMMC journey.
Need Help with Preparing for CMMC 2.0? We’ve Got You Covered.
