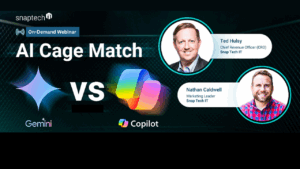
AI Cage Match: Google Gemini VS Microsoft Copilot
Keeping up with the latest AI tools can feel like a full-time job. In this head-to-head showdown, we pit Google Gemini against Microsoft Copilot to see which AI assistant delivers the best real-world results.






