Keeping Calm When Technology Fails: How to Manage Stress and Stay Productive
As we deal with stress in life and work, sometimes all it takes is a failing piece of technology to set us on edge. Keeping calm when technology fails requires us to have strategies in place to manage stress and stay productive.
How Defense in Depth Will Save Your Business from Cybersecurity Breaches and Data Loss
Defense in Depth is a cybersecurity strategy that involves layering multiple security measures across various layers of your IT environment and organization’s practices. Instead of relying on a single line of defense, such as a firewall or antivirus software, Defense in Depth implements multiple layers of protection to create reduce risk and increase resiliency, improving your security posture.
Discover how Defense in Depth will save your business from cybersecurity breaches and data loss.
Windows OS and CrowdStrike Outage Highlights the Need for Resilient Tech Strategies
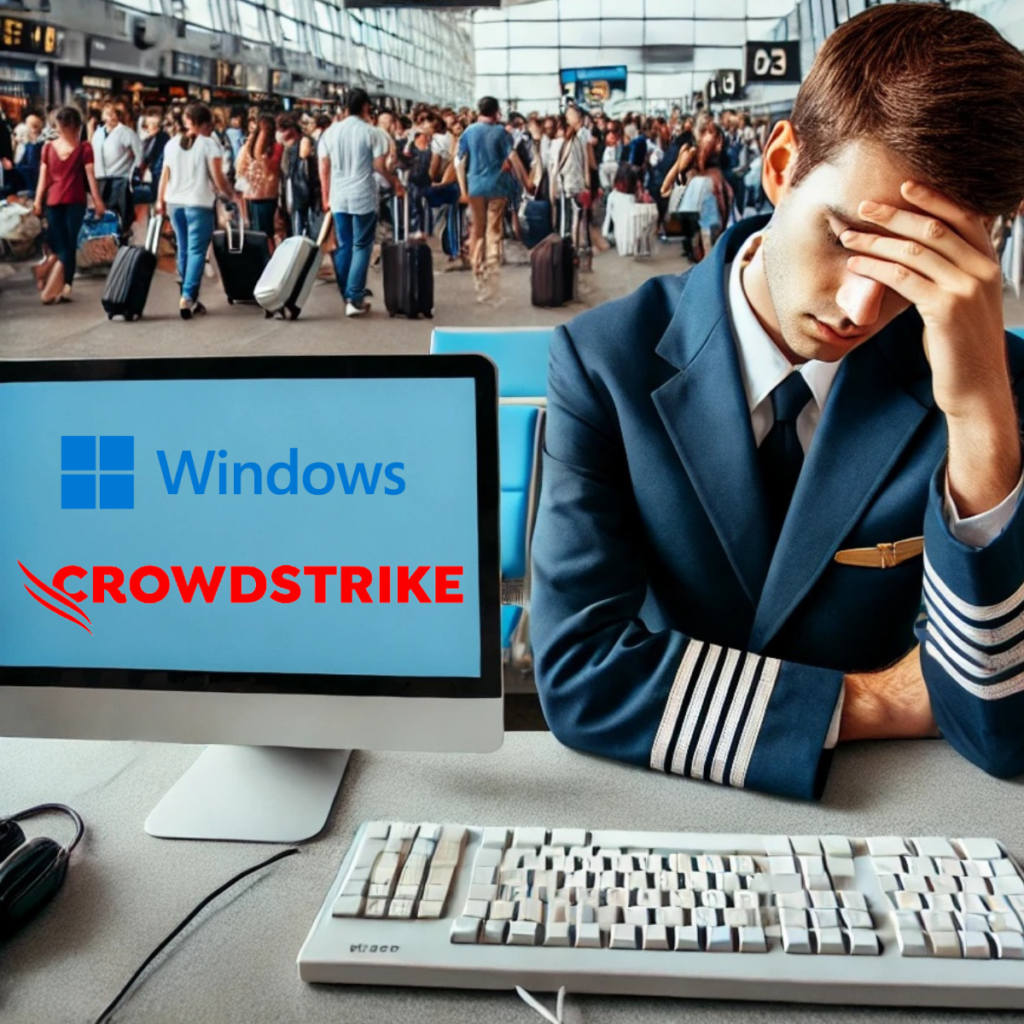
Although Cyber Risk sounds exclusively technical, many dangerous risks are introduced by non-technical methods. Technical risks include vulnerabilities in your software, unpatched or out-of-date systems, and insufficient cybersecurity measures. Non-technical risks involve human interaction such as getting tricked by a phishing scam, accidentally sharing sensitive information, or lacking secure best practices within a business. To effectively reduce cyber risk, businesses need to adopt a holistic approach that embraces both improving your tech and your training.
Beware the Monster Under Your Tech: How to Expose a Hidden Cyber Criminal

Although Cyber Risk sounds exclusively technical, many dangerous risks are introduced by non-technical methods. Technical risks include vulnerabilities in your software, unpatched or out-of-date systems, and insufficient cybersecurity measures. Non-technical risks involve human interaction such as getting tricked by a phishing scam, accidentally sharing sensitive information, or lacking secure best practices within a business. To effectively reduce cyber risk, businesses need to adopt a holistic approach that embraces both improving your tech and your training.
Reducing Cyber Risk in Your Business with Tech and Training

Although Cyber Risk sounds exclusively technical, many dangerous risks are introduced by non-technical methods. Technical risks include vulnerabilities in your software, unpatched or out-of-date systems, and insufficient cybersecurity measures. Non-technical risks involve human interaction such as getting tricked by a phishing scam, accidentally sharing sensitive information, or lacking secure best practices within a business. To effectively reduce cyber risk, businesses need to adopt a holistic approach that embraces both improving your tech and your training.
The Power of Visual Content: How Your Business Can Benefit from AI-Generated Images and Videos

According to Trend Reports, between 65 and 85 percent of people describe themselves as visual learners. Text alone isn’t enough to attract your audience and effectively convey your message. Visual content is a necessary staple of effective communication and marketing strategies. Whether you’re engaging with coworkers, prospects, or customers, the use of images and videos can significantly enhance your messaging, drive engagement, and ultimately, boost your business success.
Navigating Cyber Liability Insurance

In the fast-paced digital landscape of 2024, businesses face an ever-evolving array of cyber threats, prompting the need for robust risk management strategies. To shed light on the complexities of cyber liability insurance, Snap Tech IT recently hosted a series of Lunch and Learn events across three cities, featuring local insurance experts who provided invaluable insights into the cyber insurance landscape.
Complexities of Cyber Insurance

In today’s digital landscape, the rise of cyber threats has led to a growing reliance on cyber insurance as a crucial component of risk management strategies. Recently, Snap Tech IT hosted a webinar featuring esteemed guest speaker Joseph Brunsman, an expert in cyber insurance and risk management. Brunsman’s comprehensive overview delved into the intricacies of cyber insurance, shedding light on coverage, limitations, and the evolving landscape of the cyber insurance market.
The Top 5 Benefits of Outsourcing IT Services for Small Businesses

Small businesses everywhere are facing the challenge of how to manage their IT infrastructure and cybersecurity effectively while remaining focused on their core business.
As a small business with limited resources, trying to manage IT services on your own can put you in a constant dilemma of where to spend the next dollar and where to place your next resource. Do you dedicate it to your business purpose? Or do you dedicate it to your IT services team?