Seven Key Steps to Securing Remote Workers
In today’s rapidly evolving work environment, remote work has become crucial for many organizations. However, with this increased flexibility comes a heightened need for robust security measures to protect sensitive data and mitigate potential cyber risks. Join us for an insightful webinar as we explore the seven key steps to securing remote workers effectively.
In this webinar, we will explore: How to assess remote work risks, Why identity and access management (IAM) is one of the most important cybersecurity considerations and so much more.
Comprehensive Risk Assessment Process
Understand your Vulnerabilities Assessments of security risk require a methodical approach that begins with knowing your critical security gaps. One of the best ways to identify those critical gaps is to complete a no-cost Rapid Security Snapshot that pinpoints top risk areas that leave your environment exposed to damaging cyber threats. With your Rapid Security […]
Exploring the Security Posture of Legal Firms

The American Bar Association’s 2021 Legal Technology Survey Report shines a light on security gaps among small to medium-sized firms that expose vulnerabilities, leading to sensitive data breaches, loss of billable hours & reputational damages. Explore key findings & learn simple tips to neutralize your risk.
Zero-Click
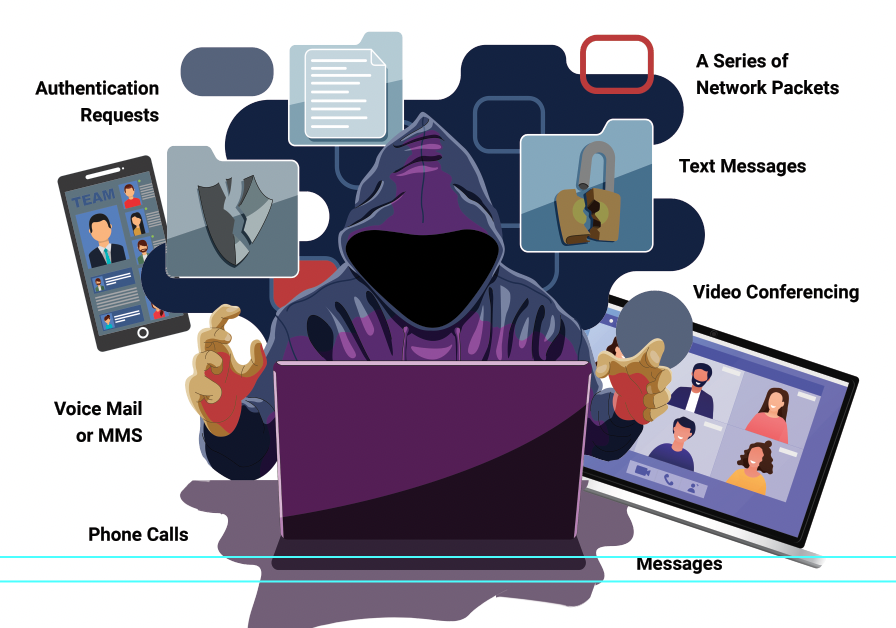
The cyber-attacks threat continues to intensify for businesses all across the United States. A method known as Zero-Click hacking is becoming increasingly prevalent, often pushed by governments onto individuals and activist groups. This is key, since phones are often the method of entry, which, in many cases, is tied to system networks. Learn more about how these attacks work and what you can do to minimize your risk exposure.
Financial Compliance and Data Security

Financial Compliance-More than most types of business, financial management firms carry a heavy burden to avoid cybersecurity risk and protect their client’s sensitive information. This is because cyber criminals mark them as a high-value target, which in turn leads to the needs for IT compliance.
Virus Alert: How to Protect Your System from Lnkr Vulnerability

Did you know that there is a new type of cybersecurity threat that your Antivirus and Firewall won’t catch? As we began implementing threat detection in our internal systems, we discovered a new type of security threat that a firewall or antivirus is unlikely to catch. It’s known as Lnkr vulnerability and its currently making […]
Colonial Pipeline Cyber-Attack: Understanding the Threat

With the recent fallout surrounding the Colonial Pipeline breach felt across much of the country, I think it’s important that businesses embrace key takeaways on the techniques used in this attack and heighten our sense of awareness to detect when things are going wrong in our environment. Educating ourselves on the many shared techniques of […]
Consulting Firm

The Firm had a very familiar problem that a lot of companies have, Bandwidth. With no true IT department or security policy in place, they were left vulnerable to cyber-attacks.
4 threats, chances are you’ve never heard of them

As new tactics consistently emerge within social engineering, here are 4 more to help you spot threats before your systems are compromised. Here we go!